Speakers and Talks

Jimmy Ahlberg
Talking tech to legal: part 2
How to talk to your lawyer about FOSS (foss-north 2025)
-
Speaker interview (.ogg, 12:54 min)
-
YouTube
-
PeerTube
-
Talk Slot
The speakers have long experience in talking tech to legal and legal to tech. In this talk we will present common mistakes, misconceptions and present an easy strategy to ease the communication between your legal team and your engineers.
Jimmy is Expert and Senior Legal Counsel for Software, AI and Standards at Ericsson. He was previously the Director of Open Source Policy with the Ericsson OSPO. Jimmy Ahlberg is also currently he chairperson of the OpenChain projects governing board.

Costa Alexoglou
Building a pair-programming app in public with Rust
This talk explores what it takes to build an open-source remote pair-programming desktop app. While building Hopp, we learned valuable lessons; from measuring video latency to understanding WebRTC internals and encoders.
We'll also discuss the attention economy and how pair-programming can help combat our fragmented attention spans.
An Engineer at Grafana Labs, he is passionate about crafting the future of observability.
Also one of the main maintainers of Hopp, the best OSS remote pair-programming app.

Pablo del Arco Ortiz
Multi-Cloud Without the Myth: What Actually Works in Practice
“Multi-cloud” is often sold as a silver bullet—but in practice, it’s complex, expensive, and frequently misunderstood. This talk cuts through the hype and focuses on what actually works. We’ll break down real multi-cloud and hybrid patterns that succeed, why others fail, and how open-source platforms like OpenNebula enable interoperability without duplicating complexity. If you’ve been promised multi-cloud freedom and delivered operational pain, this session will resonate.
Pablo del Arco is a Cloud-Edge Innovation Engineer based in Valencia, Spain, with deep expertise in Kubernetes, cloud infrastructure, IoT, and virtualization. He has extensive hands-on experience architecting and managing private and edge clouds, as well as integrating AI applications into cloud environments.
A passionate open-source advocate, Pablo actively contributes to the broader community of cloud and edge builders. He was a speaker at FOSDEM 2026 in the Virtualization & Cloud Infrastructure devroom and regularly publishes practical guides on homelab environments, alongside in-depth technical articles covering cloud federation, edge computing, and AI infrastructure.

Hans Bak
From Inventory to Inspection: What the CRA Means for OSPO Maturity
Most organisations today can generate an SBOM. Far fewer have built the systems needed to continuously verify one.
For years, SBOMs have been treated as inventory artefacts — documents produced when procurement asks, when risk management escalates, or when due diligence requires evidence. But the Cyber Resilience Act changes the expectations placed on organisations. It shifts the question from “Do you have an SBOM?” to “How was it produced, what does it miss, and can you defend it?”
This shift exposes a deeper maturity challenge for Open Source Program Offices. Modern software is not merely assembled from declared packages. Code is copied, modified and embedded. Security primitives and cryptographic functions appear without formal dependency declarations. AI-assisted development accelerates reuse without improving traceability. Package- level tooling captures declared metadata; it does not verify what is actually present in the codebase.
Under CRA scrutiny, that distinction matters. An SBOM built purely from declared dependencies may be technically correct yet materially incomplete. Cryptographic transparency requirements (CBOM), supply chain risk management expectations, and emerging audit practices increasingly demand inspection, not just inventory. This session explores the evolution from static documentation to continuous verification in modern software governance.
Experienced advisor with a track record of pioneering enterprise-level conversations around open source license compliance, security, FOSS risk management, and software composition analysis — disciplines that predate and directly informed today's SBOM requirements and Cyber Resilience Act mandates.

Alexandra Betouni
Building Open Source Embedded UIs with Qt & Slint
Qt and Slint both offer powerful open-source paths for creating embedded user interfaces, each with different focuses, strengths, and licensing models. In this talk, we’ll walk through practical examples of building basic UI components in both frameworks and explore the key considerations when adopting them in embedded products. We’ll look at architecture differences, performance implications, development experience, open-source availability, and build-time/runtime footprints. The goal is to help developers understand where each framework fits best in real-world scenarios, so they can make informed decisions aligned with their device constraints and product goals.
Alexandra is the CEO of Extenly, a UI software consultancy specializing in embedded user interfaces and an official partner for both Qt and Slint. With over a decade of experience in Qt development, she began her career building award-winning UI applications for BlackBerry 10 OS and medical devices. Her journey later took her into the automotive world, where she contributed to Mercedes-Benz’s MBUX system and played a key role in creating Neptune 3 UI, the reference interface for the Qt Automotive Suite.
A passionate advocate for elegant and maintainable UIs, Alexandra has authored Qt/QML online courses and was recognized as a Qt Champion in 2024 for her contributions to the community. Today, she leads her team in helping companies deliver beautiful, high-performance UIs across automotive, industrial, and IoT sectors.

Emiel Brok
Open by Choice, Sovereign by Design
Digital sovereignty is no longer just a strategic preference; in 2026, it is a regulatory imperative. While the "why" of sovereignty is clear, the "how" remains a challenge for many European enterprises.
In this session, we explore how open source is uniquely positioned to deliver true autonomy. We will move beyond theory to discuss the practical implementation of transparency and reusability, focusing on:
- Policy as a Catalyst: How Open Source facilitates compliance with the Cyber Resilience Act (CRA) and NIS2.
- Security through Collaboration: Enhancing resilience by leveraging the "Power of Many."
- Measuring Mastery: A practical look at how organizations can use the Cloud Sovereignty Framework (CSF) to assess their current posture across 8 key objectives—from supply chain to data & AI.
Attendees will be introduced to a privacy friendly assessment tool that allows them to benchmark their sovereignty score against EU standards and generate an actionable gap-analysis report. Let’s Dance, not Fight!
Emiel Brok is a seasoned Digital Sovereignty & Open Source Ambassador, and a prominent voice in the European FOSS ecosystem. He is actively involved in DOSBA (Dutch Open Source Business Association) and APELL (European Association of Next Generation IT Providers), where he works at the intersection of policy, community, and business strategy to promote European digital autonomy.
Known for his high-energy delivery and ability to translate complex regulatory frameworks (like CRA and NIS2) into actionable human stories, Emiel is a frequent speaker at international events. He is a passionate advocate for the "Power of Many," encouraging the ecosystem to move past compliance hurdles and embrace a philosophy of "Let’s Dance, not Fight!"

Gerhard de Clercq
Litterbox: Somewhat Isolated Development Environments
This presentation will introduce litterbox.work, a new open source utility for more secure software development inside sandboxes. Litterbox leverages Podman to easily create and manage sandboxes which provide some isolation between a host and a development environment. The goal here is to minimise damage in the event of a supply chain attack or similar.
The presentation will cover the motivation for and inner workings of Litterbox alongside a discussion of how its developer currently uses it for their own development work.
Gerhard currently works as an Embedded and Digital Systems Engineer at LNF in Gothenburg. He has a broad background in electronics spanning both software and hardware domains. However, he is most passionate about the intersection between these domains.

Ludovic Dubost
CryptPad: End to End encrypted collaboration can be easy to use
CryptPad is a collaborative office-suite that is end-to-end encrypted and fully open-source.
The project has been operating for over 10 years and has:
- more than 2000 instances installed in the World
- a flagship instance with free and paying usage at CryptPad.fr with more than 3M pads open per month by more than 300k users
- many NGO using CryptPad to protect their forms thanks to the e2ee CryptPad Forms
In this talk we will introduce the product and its suite of applications. We will highlight some important aspects of CryptPad:
- privacy is important and end to end encryption is key to achieve it
- end-to-end encrypted collaboration can have a familiar UI/UX
- end-to-end encrypted collaboration can be easy to use
We will also present the recent achievements of the project, the financial situation of the project and our plans looking ahead.
Creator of XWiki and CEO of XWiki SAS, I'm the gentle organizer of the XWiki SAS company for now 20 years, and lead the business side of the CryptPad project.
XWiki SAS, a European company based in France and Romania, only building free & open-source software leads the development of the XWiki Software used by thousands of organizations and helps companies and organizations all over the world organize, share, and collaborate on content. XWiki also leads the development of CryptPad, the E2EE Real-time Collaborative Suite, including Simple pads, Office document Editors, Drive, Online Forms and more.
A graduate of Ecole Polytechnique (X90) and Telecom Paris (95), I started my career as a software architect for Netscape Communications Europe. After being a CTO of an Internet usage analysis startup during the Internet Bubble and understanding how it works, I joined the FOSS movement.
I've been a speaker at various events including Paris Open Source Experience, FOSDEM, OW2 Conference, JDLL, Capitole du Libre, speaking about Collaboration Software, Financing FLOSS software and Privacy Solutions.
I'm also member of the OpenFoodFacts board.

Ludovic Dubost
Building Open Source and living from it without selling your soul
Subtitle: 20 Years of XWiki and CryptPad:
Competing to propose Open Source Collaboration solutions against multi-billion companies is a challenging endeavor. But it's not a technical one. While your users will demoralize you showing you all what you miss compared to your proprietary competitors having deep pockets to fund their R&D, you'll think that Open Source software is just not good enough.
But the real issue is not technical, it's economical and financial. Over the 20 years of XWiki and CryptPad, we have been able to measure what we miss for Open Source to be able to provide end user applications respecting user's Freedom and Privacy.
We have also been able to see how the changes of price or conditions of competitors have brought us more customers allowing us to increase the funding of our Open Source software
Creator of XWiki and CEO of XWiki SAS, I'm the gentle organizer of the XWiki SAS company for now 20 years, and lead the business side of the CryptPad project.
XWiki SAS, a European company based in France and Romania, only building free & open-source software leads the development of the XWiki Software used by thousands of organizations and helps companies and organizations all over the world organize, share, and collaborate on content. XWiki also leads the development of CryptPad, the E2EE Real-time Collaborative Suite, including Simple pads, Office document Editors, Drive, Online Forms and more.
A graduate of Ecole Polytechnique (X90) and Telecom Paris (95), I started my career as a software architect for Netscape Communications Europe. After being a CTO of an Internet usage analysis startup during the Internet Bubble and understanding how it works, I joined the FOSS movement.
I've been a speaker at various events including Paris Open Source Experience, FOSDEM, OW2 Conference, JDLL, Capitole du Libre, speaking about Collaboration Software, Financing FLOSS software and Privacy Solutions.
I'm also member of the OpenFoodFacts board.
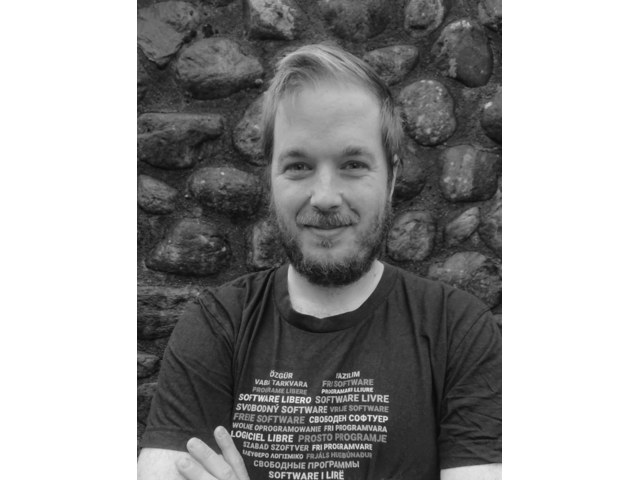
Harald Eilertsen
The Duke and the Beastie - Improving OpenJDK support for FreeBSD
Fediverse: harald@hub.volse.no
-
Speaker interview (.ogg, 10:15 min)
-
YouTube
-
PeerTube
-
Talk Slot
The OpenJDK BSD port has been slumbering in an out-of-tree existence for years. About a year and a half ago I was contracted by the FreeBSD Foundation to improve the port on FreeBSD, and ultimately try to get our changes accepted upstream.
In this talk I will present the current state of the project, and a bit about how we got here – but also some lessons learned from taking on such a big project and trying to upstream it.
Harald Eilertsen is software developer and information security professional. He has been programming computers since the early 1980's, and has worked for companies like Tandberg, Cisco, Modirum and Automattic. He is currently self employed and working as a contractor for the FreeBSD Foundation and others.
He is a core contributor to the Hubzilla open source project and a FreeBSD ports committer.

Glenn Eriksson
Digital disruption in the public transport sector through open source community engagement
The public transport sector is mostly a traditional sector with an oligopolistic market situation for system solutions for travel planning and ticketing. The lock-in and dependency to few system vendors in Europe stifles innovation and impedes initiatives to make public transport more attractive. But in the Nordic countries, public transport agencies (PTA) choose an alternative path to overcome system vendor dependency through open source and by engaging in community development. By choosing open source and engaging in community development they achieved political objectives to make public transportation an attractive alternative to car travelling. Our qualitative study interviewed 13 persons from 5 different PTAs, freelancers and consultants firms in the Nordics, entailing an alternative pathway which digitally disrupted the regional or national public transport market.
Our study presents a model on how organisations can co-evolve with the open source community through long-term engagement to access state-of-the-art digital technology and foster innovation. The model depicts a cumulative process that yields better opportunities the longer and deeper the engagement becomes. This enables digital transformation outcomes such as access to a global pool of knowledge, agile and adaptive value-creation, open innovations processes, partnership and synergy opportunities. The talk will present the findings from the study and how the model can be used as a tool to better understand and depicts the organisational alignment process, the inner mechanism and the possible transformative outcome of engaging in open source community development. Our findings demonstrate that also large traditional organisation within the transport sector can partially foster digital transformation capabilities through departmental engagement in community development which can radiate to other parts of the organisation. This entails alternative pathways for traditional organisation that are under demand to digitally transform. But this requires sustained resource investment and loyalty to community objectives to gain influence and trust, to access deeper collaboration and innovation opportunities. The session ends with discussion and Q &A about obstacles, possibilities and strategies when engaging in open source community development. Especially concerning the public sector on how they can be more involved and engage in community development.
Researcher focusing on open source community development and how participation can facilitate building digital transformations capabilities and foster engagement in open innovation processes.

Evilham
Running a FOSS associative ISP
Whether neighbourhood mesh networks, Fiber To The Home or Data Center services: eXO.cat, a Barcelona-based associative ISP, offers these as a volunteer-run entity with a decision-making process marked by general assemblies and consensus amongst smaller workgroups.
We would like to share how we operate with FOSS, community, transparency and openness as core values, leading to a stable entity that helps promote other software and community projects.
Evilham does computer things professionally and for fun things like pottery, swimming, singing, dancing or woodworking. As the current treasurer of eXO.cat, Evilham helps with many things behind the scenes as well as other more “traditionally technical” tasks

Jeremiah Foster
Modern Email
IETF's charter says: "Internet Messaging (“email”) is one of the oldest applications still supported by the IETF. It consists of numerous layers and extensions that support the robust construction, transport, retrieval, and interpretation of messages."
Email is foundational to the modern internet but has not changed much until recently. With the growing interest in self-hosting and sovereignty, there is a renewed effort around email both from organizations like ICANN and the IETF, as well as new open source and Free Software for serving, sending, and reading email.
Collaboration tools are also expected by email clients as well so email servers have to support much more than "just" email, they have to support logging in to distributed systems, encryption, files, calendars, contacts, and even arbitrary blobs.
The underlying technologies and protocols for email are changing too. SMTP and IMAP are complex, showing their age, and scale poorly. The new JMAP standard shows promise and will hopefully remove some cruft. Even mbox and Maildir are on their way out as email servers scale to billions and adopt object storage, key/value stores, and more modern databases. Even PGP has a new implementation in Rust called Sequoia which improves security of email via memory safety. Spam fighting is key to modern email and there are new techniques and tools like Rspamd.
We'll do a quick survey of what's available in terms of Mail Transfer Agents (MTAs) and Mail User Agents (MUAs) including Webmail. We'll briefly touch on Collaboration servers as well.
Lastly, we'll take a look at some of the things the future might bring and point to some RFCs so that one can create one's own tools.
TBD

Magnus Glantz
Running an open source project like a professional
Join this session which details Red Hat's secrets to success for creating and running successful open source projects.
Red Hat has experiece of running some of the worlds largest and most successful open source projects since the 90s. This session is jam packed with Red Hat's hardened and battle proven practices.
Magnus works as a Principal Specialist Adoption Architect at Red Hat. He works to increase successful adoption of open source solutions from Red Hat in EMEA. He also sits in the board of Open Source Sweden and APELL, The European Open Source Software Business Association.

Magnus Hagander
PostgreSQL Don'ts and Dos.
PostgreSQL continues to be one of the most popular choices to back applications today. And in this, a lot of people end up running with unadjusted defaults or bringing over both application and database tuning from experiences with other systems. In this presentation we'll go over some of the more common mistakes or suboptimisations I've come across when working with many different clients over the past couple of years, and what to do to adjust them. I twill be covered with a mix of developer and DBA perspectives, as these often go hand in hand.
Magnus Hagander is a member of the PostgreSQL Core Team and a developer and code committer in the PostgreSQL Global Development Group. He currently serves as President of the board for PostgreSQL Europe.
Magnus is one of the original developers of the Windows port of PostgreSQL. These days, he mostly works on other parts of the PostgreSQL backend, recently with a focus on security features such as authentication and encryption.
He is also one of the core members of the postgresql.org infrastructure team, maintaining the servers that power the project, and one of the maintainers of the postgresql.org website, and the lead maintainer of the NPO/conference management system used by most PostgreSQL community events.
He's been a PostgreSQL user since version 6 (with some non-serious use of Postgres 95 before that), and currently serves on the Core Team and as President of the Board for PostgreSQL Europe.
To pay the bills, he is a PostgreSQL and open source software consultant at Redpill Linpro in Stockholm, Sweden, where he works on consulting, support and training services, as well as custom development work.
Ishan Jain
What did AI just do? Making LLMs Observable with OpenTelemetry
AI systems don’t crash; they misbehave. And when they do, logs and metrics alone won't tell you why. Whether you're building with GPT, open-weight models, or RAG pipelines, one question keeps coming up in production: “What did the AI just do?”, “Why did it respond that way?”, “Why is this prompt slower than before?”, “Why did our bill triple overnight?”
This talk is about making AI systems observable, not just at the infrastructure layer, but at the model behavior layer. Using OpenTelemetry and open-source tooling like Jaeger and Prometheus, we’ll walk through how to trace prompts, monitor costs, detect drift, and correlate weird model behavior with your application flow. If you're deploying AI into real systems and want visibility that goes beyond “Something went wrong”, this talk will give you the frameworks and tools to stop guessing and start understanding.
An ex-rocket science student turned SRE and now a Developer Experience Engineer at Grafana Labs, I am a core maintainer for the Grafana Ansible Collection and the Grafana Operator, with over 2 million downloads combined.

Olle E. Johansson
SBOM today: What is the state of SBOMs?
The EU Cyber Resilience Act is built around supply chain security with an SBOM in the middle of it all. What is an SBOM? What's the problem it is trying to solve and what is the status of the world of SBOMs?
Olle will take you through what the expectations are and where the reality is today, and give some practical examples on open source tools to use.
Olle is active in OWASP, OpenSSF, ORCWG and in his own garden during summer. He is also co-founder of the SBOM Europe project
Lucas Lasota
Interoperability goes to court: a case for Software Freedom
As society grows in complexity, interoperability becomes inevitable. However, large corporations resist implementing interoperable solutions when their assets become important enough to be subject of regulation. This happened with Apple, which as soon as the European Union decided to regulate how interoperability should be handled for Apple's mobile operating systems iOS and iPadOS, the company decided to sue the regulator claiming interoperability is disproportional to fundamental rights.
The Free Software Foundation Europe (FSFE) decided to intervene in the case, demonstrating that Apple is being regulated due to the public interest, and the legislation in case (the Digital Markets Act) should be enforced in a Free-Software-developer friendly way.
The audience will learn how interoperability regulation is key for Free Software, as it allows developers to access features and functionalities in proprietary operating systems which were exclusively controlled only by Apple.
The talk will be held in English. No prior knowledge is required.
Dr. Lucas Lasota, MA, PhD, is a researcher, lecturer, qualified lawyer (Brazil) and project manager in the field of IT, telecommunications and contract law. His research focuses on regulatory measures of digital technologies and their impact on individual and collective rights, as well as on internet governance, telecommunications and international contract law. He works as a researcher at the University of Halle Wittenberg and as Legal Programme Manager at the FSFE.

Johan Linåker
Digital sovereignty through open source – Europe’s strategic opportunity
Digital sovereignty—the ability to control and influence one’s digital future and infrastructure—is increasingly at the centre of political and technological agendas. Recent signals, such political signals and shifts in attitude toward non-European cloud providers, underscore a broader momentum. While governments pursue different and sometimes overlapping strategies, open source consistently emerges as a key enabler. Through open strategic autonomy, sovereignty can be gained while fostering interoperability, reuse, and collaboration. Open source provides a path to influence without requiring exclusive ownership, balancing self-reliance with global interconnectedness.
However, leveraging open source effectively requires capabilities and know-how across society and industry. This implies actions at multiple levels: cross-cutting training and workforce development, sustainable business ecosystems, supportive policies and OSPO structures in both public and private sectors, long-term procurement strategies, targeted government facilitation and funding, and investments in the maintenance of foundational technologies. Strategic planning is essential to align these capabilities with societal and industrial goals. This talk will delve into how Europe can grow Digital sovereignty through open source, and leverage the strategic opportunity it provides.
Johan is a senior researcher at RISE Research Institutes of Sweden with focus and passion for open source software, data, gov and innovation. Co-founder and community manager for NOSAD.se.

James Lowden
The Once and Future COBOL
GCC 15 for the first time included COBOL among the languages it compiles.
The reader may well wonder why a small company would devote years of development to produce a product they don't own and can't sell. The reader might also wonder why GCC decided to include COBOL. In short, what use is COBOL?
To those questions and more, we have answers.
As Mark Twain said of himself, news of COBOL's demise is much exaggerated. Industry studies show billions of lines of COBOL still in production. With a probability of 95%, your last ATM transaction went through a COBOL application. Not for nothing did nearly every large firm pull out all the stops 30 years ago to add two digits to the date, to adapt their critical software to the 21st century. They didn't do that to throw it all away. It still chugs along.
COBOL remains useful because it was specifically designed for its problem domain. No language is better suited for nuts-and-bolts unglamorous data processing. For example, COBOL defines an I/O model, numerical precision, 8 forms of rounding, and over 100 runtime exceptions.
Programming languages often have shallow, undeserved reputations. Lisp has too many parentheses, COBOL too many words, Perl is write-only. Let's talk about why COBOL remains viable and vital, and why it's now part of GCC.
James spent most of his career on Wall Street in quantitative research systems and databases. Today he's leads the GCC COBOL project, building a ladder to let companies escape their walled gardens.
James lives on the seacoast of Maine now, where he works from home and spends his free time in the summer, never enough, sailing the Penobscot Bay.

Bassem Nomany
Using FOSS to Protect Embedded Systems Data in Transit
Modern embedded systems are no longer isolated devices sitting quietly on a PCB. They are connected systems. They talk to the cloud. They talk to each other. They talk to mobile apps, gateways, factory networks, vehicle ECUs, and backend services.
FOSS does not make your system secure automatically. It gives you tools. Security only exists if you configure, integrate, and maintain those tools correctly.
In this talk, we’re going to explore how to use FOSS stacks in both Zephyr and Linux-based embedded platforms to protect data in transit across multiple networking layers with defense in depth.
We’ll look at different protection strategies at each layer of the stack, including application layer encryption with TLS and mTLS, network-layer protection with IPSec, link-layer security with MACSec, and segmentation and policy enforcement through firewall strategies — and how to choose the right combination using threat analysis and risk assessment.
Bassem has 13+ years of experience in embedded HW/SW development and has served as team Lead & Architect for Daimler's next-gen Infotainment platform and been a lead SW architect in several Auto OEM projects. He understands the power of free open source projects to make awesome products and contribute back.
He specializes in: Resource constrained IoT devices and RTOS. Rich UX Rich information and media systems.

David Runge
Signing distribution artifacts with Signstar
Digital signatures are used in many contexts to guarantee the authenticity of a specific artifact, that is provided by a Linux distribution. Artifacts of distributions may be package files, repository metadata, installation media, or verified boot loader components for UEFI.
When issuing digital signatures, it is pivotal to secure the private key material and ensure, that no unauthorized entities gain access to it. Community-driven distributions, similar to other small-scale social groups in software development, are usually funded by donations and are organized in a decentralized manner. For artifact signing this often leads to using cost effective, centralized approaches (subjective to vendor lock-in), or fully automated, but unsafe approaches (which may expose private key material), and/or relying on single individuals to do the task (semi-)manually.
The Signstar project provides Rust-based tooling for creating a custom, image-based operating system, that is used for the secure signing of artifacts. Based on modern cryptographic standards, cost effective HSM backends and the avoidance of central authority, it allows also small-scale development groups to create safe signing environments for their particular needs.
This talk will provide a high level overview of the Signstar project, its various components and in what contexts it can be used.
This talk is aimed at members of Linux distributions, as well as small-scale software development groups, that have a need for digital signing of their artifacts.
I am a self-employed software developer, that works on projects related to Arch Linux. Here, my field of interest is package management, as well as cryptographic signing and verification.

Henrik Sandklef
License Compliance 101
In this talk I will go through copyright, license, FOSS licenses compliance, compatibility, common mistakes
The talk will serve as an introduction to beginners but also as a heads-up for non-beginners that there be are dragons here
Born. Then grew up. Then got older

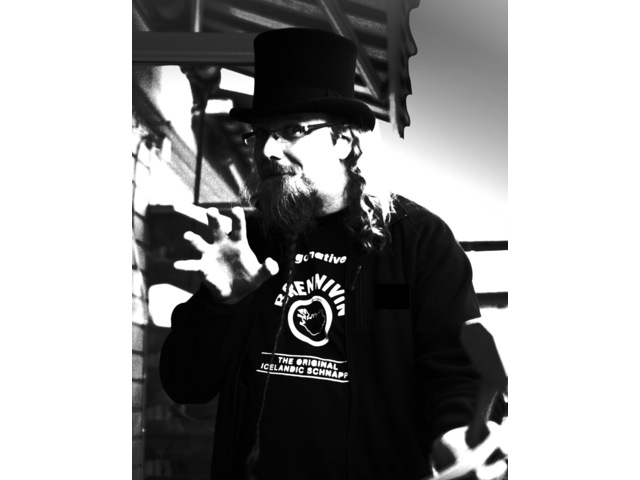
Bogomil Shopov
Disobey: FOSS tools to fight back and their adoption.
Everyone is trying to control your communication. The reasons vary from simple curiosity to pure commercial interest, all the way to using it to control one's thoughts.
Are there any ways to fight back, and why are free software and open-source tools a good alternative to the ones you use?
As cypherpunks, do we have the obligation to help people be ready for the worst, or should we only take care of ourselves? As a FOSS community do we do enough for the adoption of those protection mechanisms with our friends, family and the rest of the world?
In this talk, I will cover my experience with fighting back against #chatcontrol - what I have learned and what happened after I decided to give up. (a very short overview). Instead of losing my dignity and time with politicians, I decided to teach people how to fight back!
- The first part of my talk covers terms like zerotrust and what decentralization is.
- The second contains smart words and foss tools to protect your communication.
- The third leads you through a journey to fight the smartphone zombies by using alternative services.
- The fourth part will share some learning I had for trying people to adopt those protection mechanisms.
Take a notebook on paper to write some of it down.
Note: this talk will not be recorded.
Human. Artist. Hacker. Metalhead.
I’ve spent 20+ years in technology and 50+ in being human. I care deeply about free and open-source software, cybersecurity, ethical design, privacy, and tech that serves people. Through heavy metal and technology, I inspire others to become better humans, and remind creators to build tech that’s kind to us.
I fosstribute to Firefox, Thunderbird and OpenStreetMap. I do not represent any company! Bulgarian living in Prague. I run a Creative Commons-licensed theater show that encourages people to change the world.

Pratik Singh
Intelligent Git Companion: An LLM-Powered Storyteller for Your Commits
The problem is simple but painful: Git history is messy, fragmented, and rarely tells the why behind the what. Developers often drown in endless commits, cryptic messages, and sprawling diffs only to repeat the same confusion during code reviews, merge conflicts, or onboarding. Git should be a record of our intent, but instead it's a mess!
This talk introduces an “Intelligent Git Companion”—a LLM-powered CLI tool that stitches together commit logs, diffs, and GitLab issues/MRs into a coherent narrative. It can act as a personal aide to understand the development journey, a reviewer’s assistant to summarize another developer’s MR, or even a guide during hairy merge conflicts. It can also help teams decide when to rebase, squash, or cherry-pick commits, and extend into CI/CD pipelines to provide automated storylines for branches and deployments. Whether you’re a junior trying to make sense of history or a senior reviewing mission-critical changes, this tool turns Git into a conversation
I am a software developer with expertise in DevOps and Golang. I have worked at several companies, including GitLab, NASDAQ, Mercari Japan, HackerRank, GitHub, and JUSPAY. I am passionate about leveraging DevOps practices and tools to streamline software development processes. 😊

Daniel Stenberg
Open Source AI reality
In the booming trend of putting AI everywhere and into everything, we are told that AI soon replaces all programmers, makes Open Source obsolete while it also finds all security problems and makes writing secure code impossible.
This talk is a reality check and status update on AI tooling for security and Open Source maintenance. Ban all AI for incompetence, adopt it whole-heartedly because it does better code than humans or maybe find a middle-ground?
The curl project has been bombarded by large volumes of low quality AI slop security reports where sloppy humans cause Denial-of-Service attacks by overloading the maintainers with almost-real-looking rubbish. At the same time, AI powered analyzer tools find flaws and mistakes in existing code in ways no previous code analyzers have been able to.
This is the timeline we didn't ask for, but this is how it works.
Daniel Stenberg is the founder and lead developer of the curl project. He has worked on HTTP implementations for over twenty years. He has been involved in the IETF for twelve years and he worked on the HTTP stack in Firefox for several years at Mozilla. He participates in the QUIC working group and is the author of the widely read documents "HTTP2 explained" and "HTTP/3 explained". Employed by wolfSSL.

Gry M. Tveten
Open source tools for the power sector
The Shyft Open Source project originated in the need for a new framework for doing hydrological forecasts for the power industry in Norway. Later, it was expanded to include tools to help orchestrate power market modeling in an operational context. PyPSA is an open source project that provides everything you need to model power markets and much else related to power markets, except hydrological forecasting and orchestration.
Combining the two has potential for allowing for fully open source power market modeling with the operational reliability required by industry. This talk will present an example of how you can combine the two frameworks, the challenges related and further development needed
Gry Tveten has a background in experimental nuclear physics. During her time in research, she pushed for open sharing of scientific software used in publication and for open data.
In 2019, she switched fields and started work as a consultant in IT and data science. Her work has mostly focused on the Norwegian power industry and developing tools that support optimal use of resources.

Jelina Unger
Hybrid Multi Factor Authentication: Balancing On‑Premise Control and Cloud Integration with privacyIDEA
Centrally managed MFA with privacyIDEA (foss-north 2025)
-
privacyIDEA
-
Slides
-
YouTube
-
PeerTube
-
Talk Slot
Passwords get compromised every day, and reports of hacked accounts are increasingly prevalent. Clearly, multi-factor authentication (MFA) is the answer to enhancing security for both individuals and organizations. However, the challenges of setting up and managing second-factor authentication across multiple applications can be burdensome for IT departments, consuming valuable resources and time.
This talk introduces privacyIDEA, a robust MFA management system that centralizes the management of tokens across various applications, allowing for seamless reuse across different logins. This unified approach not only reduces the management overhead for IT departments but also significantly enhances the user experience.
privacyIDEA is designed for versatility, accommodating a broad spectrum of system requirements, which allows configurations to be tailored to meet specific organizational needs. As a deliberately on-premise solution, it empowers organizations to retain control over their data and systems. Meanwhile, the increasing shift towards cloud-based systems raises critical questions regarding the continued relevance of on-premise solutions.
In contrast to our talk from last year, we will explore in this talk the ongoing importance of on-premise solutions alongside the significance of cloud systems. We will discuss the challenges of integrating these two environments, illustrating our approach with EntraID as an example to demonstrate how privacyIDEA maintains flexibility, allowing for both an on-premise-only authentication system and hybrid environments.
Jelina is a software engineer who has been working on the open-source multi-factor authentication management system, privacyIDEA, for nearly two years. She holds both a bachelor's and a master's degree in medical engineering with a focus on computer science. Her interest in cybersecurity grew during her studies and led her to contribute to the privacyIDEA project.

Various participants
Lightning talks
foss-north lightning talks. Short talks, max 10 minutes about something fun and FOSSy. These were the talks given during the conference:
- Mingduo Lu - Backstage @ Volvo Group
- Felicitas Pankalla - The thin line between code and configuration (a YAML/Helm rant)
- John Graham - Fully Automated Luxury Standups
- Evilham - FOSS Forms: LiberaForms
- Jimmy Ahlberg - Are patents here to save FOSS?
- Simon Nielsen Knights - Fuzzy Logic Evalution
- Louis Tim Larsen - A shoutout for physical meetups - Slides

Lars Wirzenius
Distributed CI with Radicle and Ambient
Centralized systems are either vulnerable or tools of oppression. GitHub, for example, has closed accounts of people from countries the US doesn't like, or removed specific repositories Microsoft or their business partners don't like. When GitHub is down, software development around the world slows down. This has severe consequences for the impacted people, because GitHub is the expected location of much of the world's open source software. It is time to break this dependency on GitHub.
Radicle is an open-source, peer-to-peer collaboration system for software development built on top of Git. It does not require any centralized system. Radicle CI builds on top of Radicle to offer continuous integration, even distributed CI, again without centralized servers. Distributed CI means that anyone can run CI for any public project they choose and projects can choose to trust specific CI nodes. Nobody has to use a specific single server for CI. At the same time, it's easy to provide CI capacity for specific projects that need it.
This talk explains the concepts of Radicle and its CI support using the Ambient CI engine. Ambient is designed to make it safe and secure to run CI on other people's code, without having to trust the authors of that code or any of the dependencies they use.
This talk will give the audience a high level understanding of Radicle, Radicle CI, and Ambient. There will be a live demonstration. The talk will contain a project status update ("How do you compete with Microsoft's billions sponsoring 'free-for-open-source' to create vendor lock-in?") and near future plans.
This talk is aimed at all open source developers who are curious about decentralized Git.
Lars has been programming for over forty years, mostly open source. He has code running on all continents on Earth and on Mars. He contributed to the Linux kernel before it was called that. He was part of the Debian project for a very long time. He now works on Radicle, the distributed Git forge, and its CI support. In his free time he drinks too much tea and obsesses about minute details about implementing backup software.

Eirik Øverby
Dirty Tricks: Using nginx and Lua to thwart bots and skript kiddies
(Or: Fighting denial-of-service for fun and profit.)
For fun
I want to run a BBS on an old 386 machine, but exposing it to the Internet via Telnet will turn any drive-by portscan into a potential DoS (not DOS). I'm sure we've all been there. Right?
For profit
Someone realises that throwing hundreds of thousands of TLS handshakes per second at us is worth it, and I don't have more CPU to throw at the problem. That's what we get for placing ourselves in the line of fire, I guess?
Dirty tricks
So what can be done about this? Well it turns out that with Lua and Nginx, I can solve both problems. Join me for a brief excursion into the world of retro-BBSes, an introduction to some Internet Scumbags and their shenanigans, and some possible solutions to these problems.
I'm not an active Lua coder, and I don't know nginx nearly well enough despite having used it for 15 years. So here's fair warning: Anyone who actually knows these things may catch a bout of nausea.
Model '77, Slackware-gone-BSD in the early 00s, escaped the dying world of OS/2 to be doomed to death by Netcraft for another decade. Now managing jailed (but not dead!) systems for a living and as a hobby.
Mid-life crisis topic: Retro PCs.
~ love over gold ~